ZAP is dead! Long live Zap!
We take a look at the Zed Attack Proxy as it moves away from OWASP and towards the Software Security Project
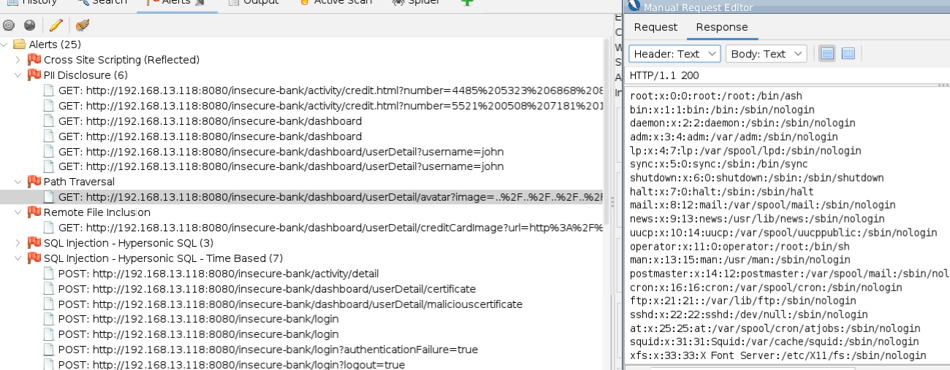
ZAP is a DAST (Dynamic Application Security Testing) tool that’s been around for over a decade and is widely used throughout the industry.
Gitlab Ultimate makes use of ZAP proxy in its paid-for Gitlab Ultimate security suite and it’s not hard to see why. It has all the configuration options you would need, which can’t be said for similar tools like PortSwigger Dastardly.
Well known and loved, ZAP is in use all over the world. It scans applications for application vulnerabilities automatically in pipelines but is also used by penetration testers to manually assess applications too.
Zap has been synonymous with OWASP since its launch, but no more.
“As an OWASP project, ZAP has greatly benefited from the exposure, significantly increasing the likelihood of people trying it out. An unexpected invitation to present ZAP at OWASP AppSec Ireland in 2012 was a major boost, and since then OWASP Conferences and Chapters all over the world have really helped spread the word about ZAP.
Unfortunately OWASP has struggled to support and invest in projects, especially big projects.
ZAP is a big project. It has grown into the world’s most popular web scanner and directly competes with commercial projects that have huge investments. We need much more investment in order to thrive, investment that SSP is committed to raising.”
Simon Bennetts - ZAP maintainer [src]
What does this mean for ZAP?
Hopefully great things, but a little disruption too.
Zap is already a fantastic tool with a wide audience (11.2k stars on Github) and over 200 contributors. It’s the poster child for opensource security tooling, and an inspiration behind many others.
Simon Bennet has dedicated over a decade to supporting ZAP, so it’s a welcome boost that he now works on it full-time under the sponsorship of the SSP. This should mean bigger, more time-consuming changes make the roadmap.
Unfortunately, ZAP is coupled to OWASP in a number of ways but the biggest issue is likely going to be its container images.
The packaged-up version of ZAP running all over the world is (in almost all cases) running from a docker container. These containers are predominately downloaded automatically from the OWASP account over at DockerHub, which to date has over 100 million downloads!
As of 2 days ago, those containers are still being updated but no one knows for how long.
Most pipelines are likely just always using the latest image, so are silently getting the latest version every time. This could soon stop, ironically exposing these users to security issues.
To address the issue now, we recommend switching to the Github hosted images.
ZAP handily provide this mapping:
| DockerHub | GHCR |
|---|---|
| owasp/zap2docker-stable:latest | ghcr.io/zaproxy/zaproxy:latest |
| owasp/zap2docker-stable:latest | ghcr.io/zaproxy/zaproxy:stable |
| owasp/zap2docker-stable:2.12.0 | ghcr.io/zaproxy/zaproxy:2.12.0 |
| owasp/zap2docker-stable:s2023-06-09 | ghcr.io/zaproxy/zaproxy:20230609-stable |
| owasp/zap2docker-bare:latest | ghcr.io/zaproxy/zaproxy:bare |
| owasp/zap2docker-bare:2.12.0 | ghcr.io/zaproxy/zaproxy:2.12.0-bare |
| owasp/zap2docker-bare:b2023-06-09 | ghcr.io/zaproxy/zaproxy:20230609-bare |
| owasp/zap2docker-weekly:latest | ghcr.io/zaproxy/zaproxy:weekly |
| owasp/zap2docker-weekly:w2023-06-12 | ghcr.io/zaproxy/zaproxy:20230612-weekly |
| owasp/zap2docker-live:latest | ghcr.io/zaproxy/zaproxy:nightly |
ZAP is dead! Long live Zap!
Punk Security will continue to use ZAP, and support our customers who use it too.
Getting meaningful results from ZAP is difficult, as it is with all DAST tools. They suffer from the same challenges of too many false positives and too few detections.
Most organisations use ZAP with the default Quick or Full scans, but their apps have authentication or third-party dependencies. The end-result is that the DAST scanner cannot identify these service issues, and cannot authenticate, and therefore lets you know that it couldn’t find anything!
Implementing DAST is not a quick or easy process, but with some effort ZAP produces some fantastic results.